TruffleHog authentication
Default
The default authentication method for TruffleHog uses Google Oauth or Magic Links for user management. Administrators must add each user by email that should have dashboard access to the Users page.
SAML SSO
Authentication can be configured to be handled by a SAML SSO identity provider (IdP). When this option is enabled, the IdP is responsible for user management.
Okta Configuration
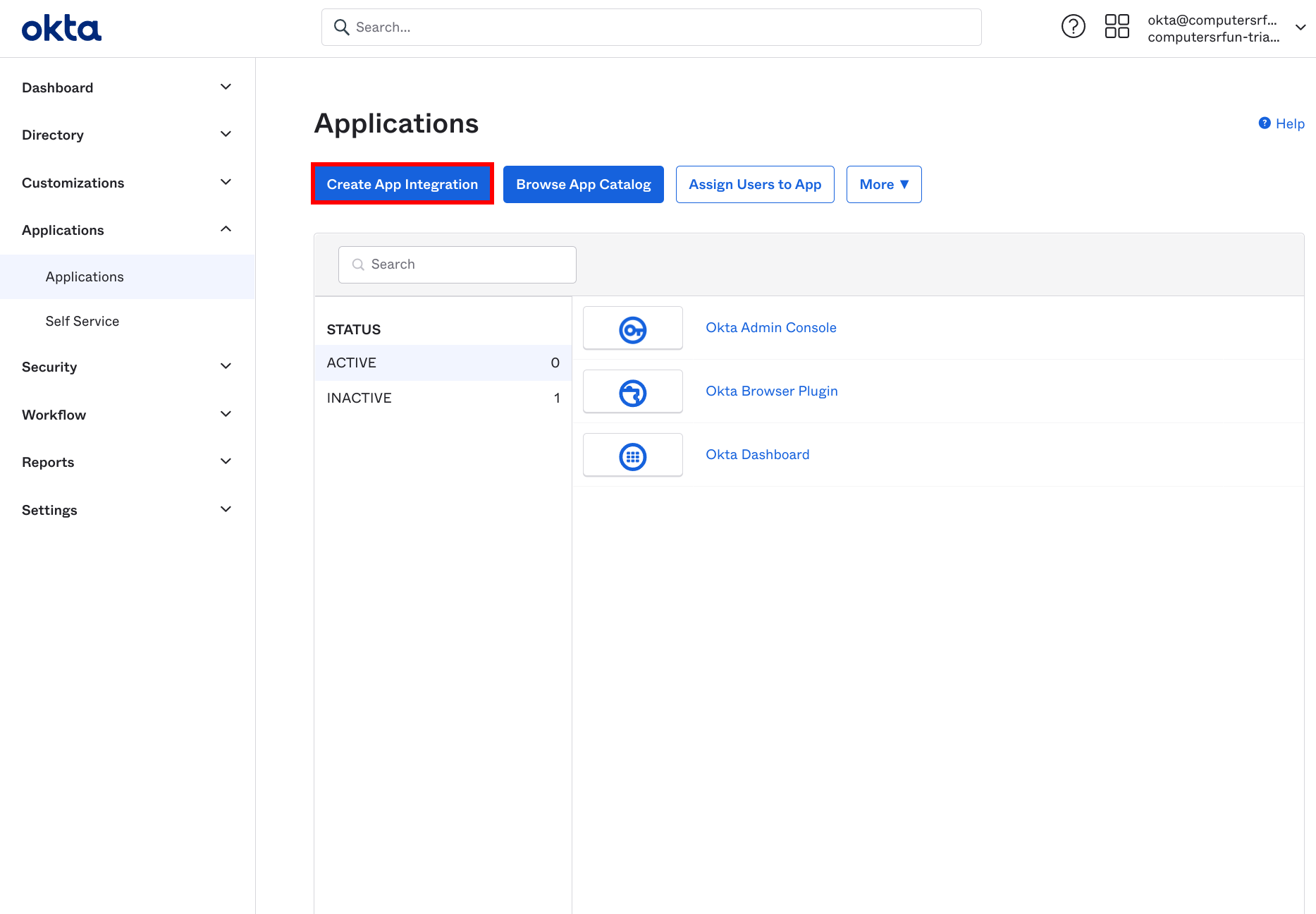
- Select “Create a new app integration”
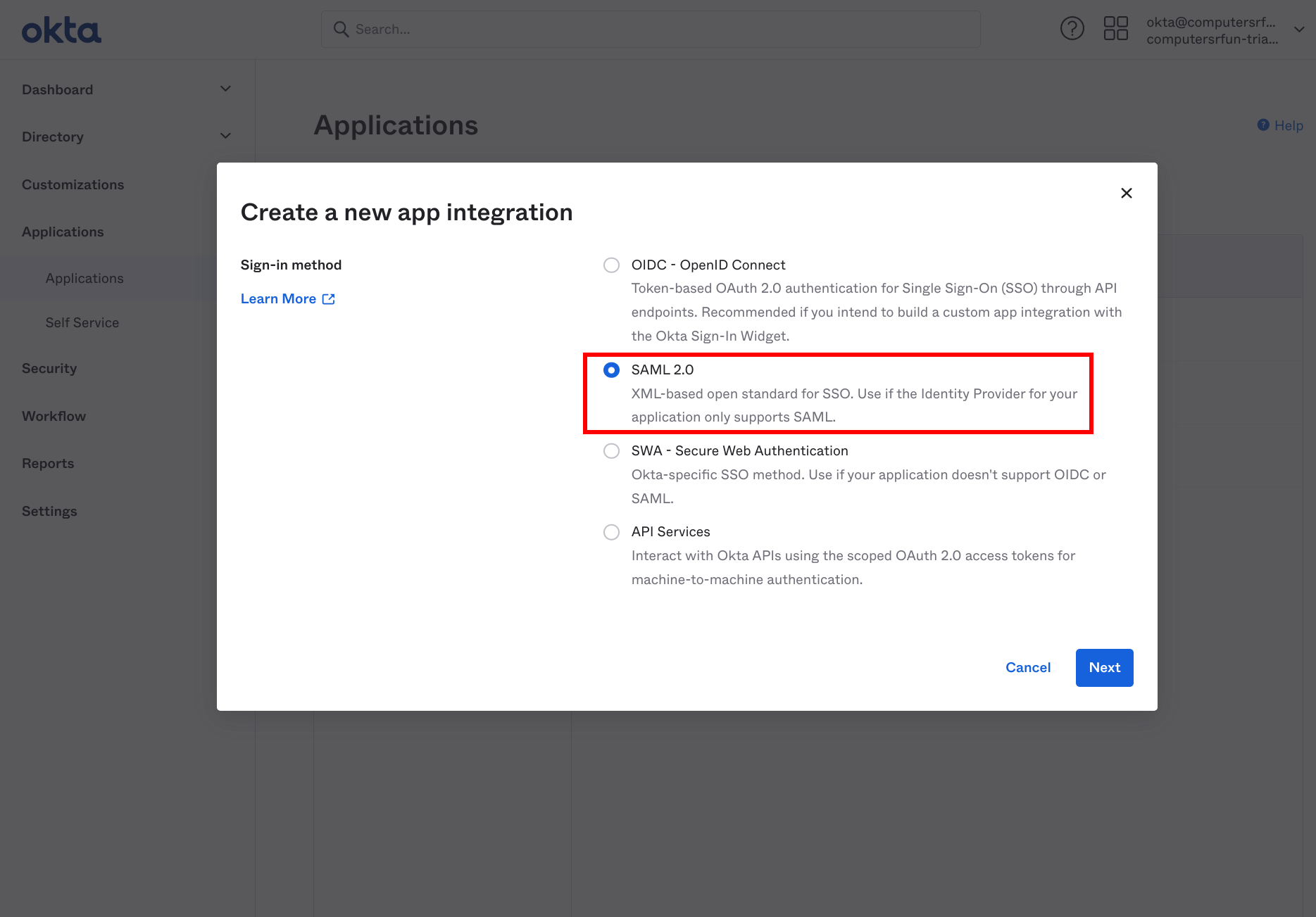
- Select a “SAML 2.0” app
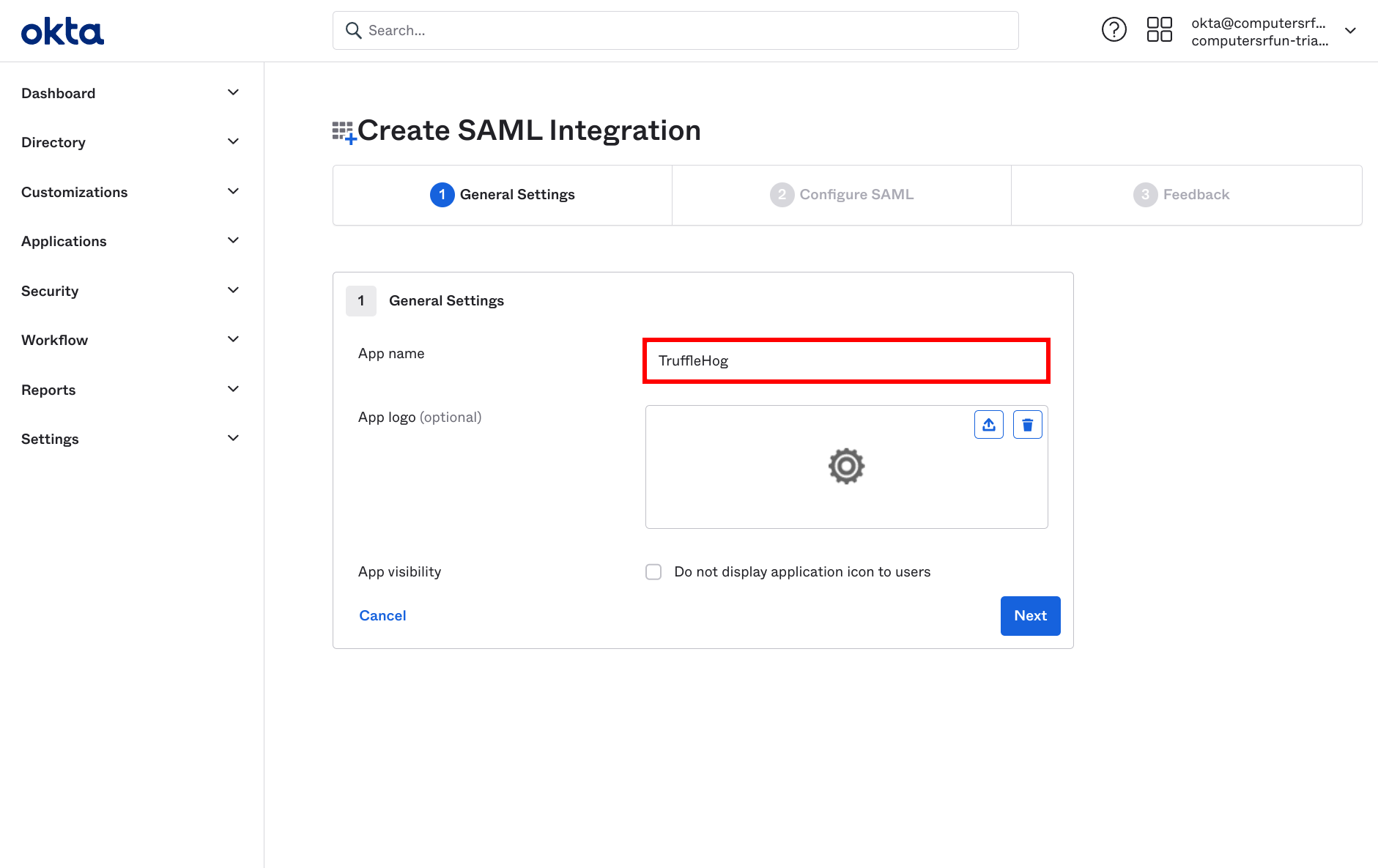
- Set your app name and app logo
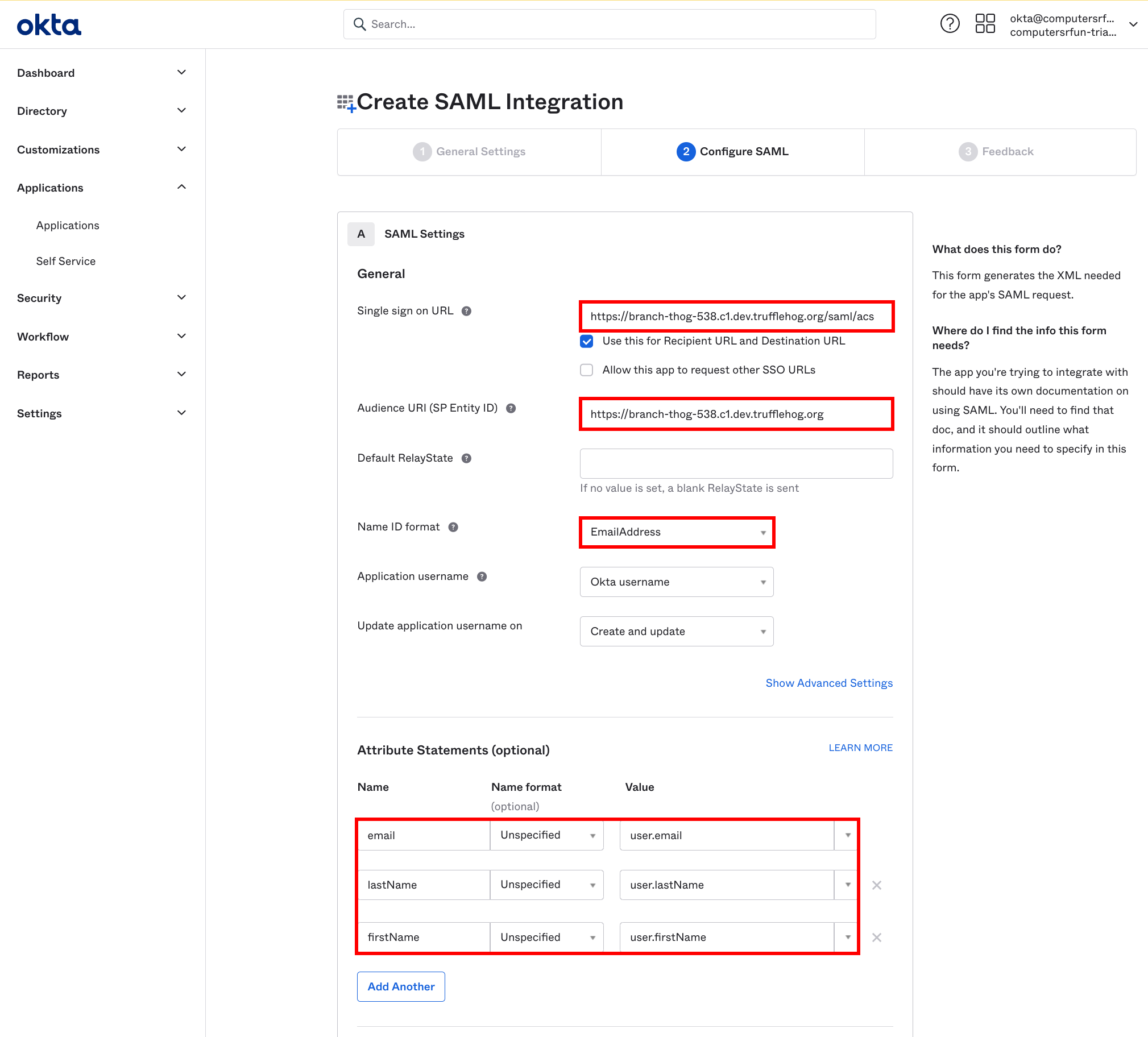
- Single Sign on URL → See Authentication page in TruffleHog dashboard
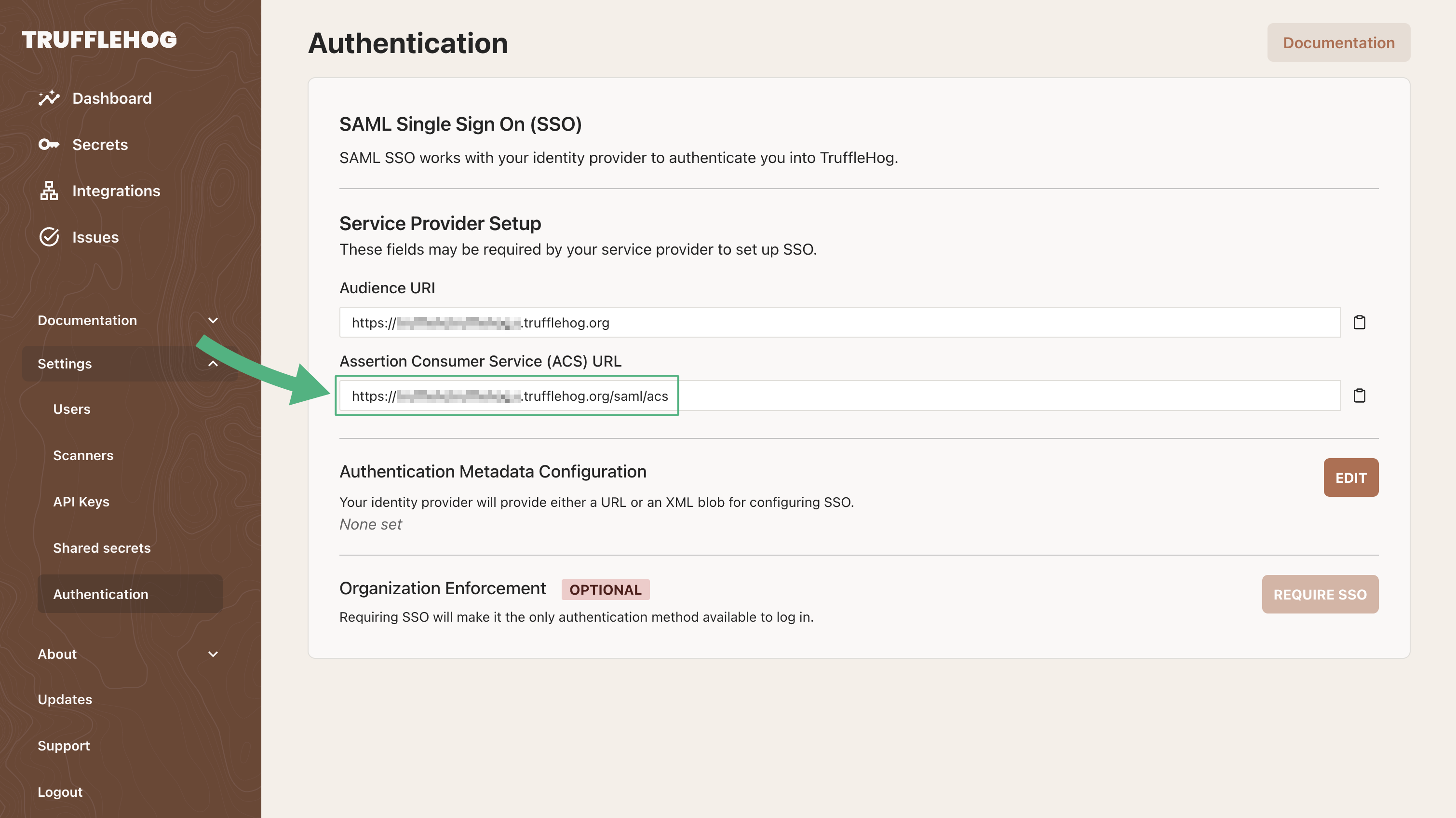
- Single sign on URL → See Assertion Consumer Service (ACS) URL on Authentication page in TruffleHog dashboard
- Audience URI → Base URL for your TruffleHog deployment. For example, if your ACS URL is https://real-strong-chipmunk.c1.prod.trufflehog.org/saml/acs, your Audience URI will be https://real-strong-chipmunk.c1.prod.trufflehog.org
- Name ID Format → EmailAddress
- Add the following Attribute Statements
- email → user.email
- firstName → user.firstName
- lastName → user.lastName
- Complete setup
- Go to the new app admin page
- Go to Sign On tab
- Open “View SAML setup instructions”
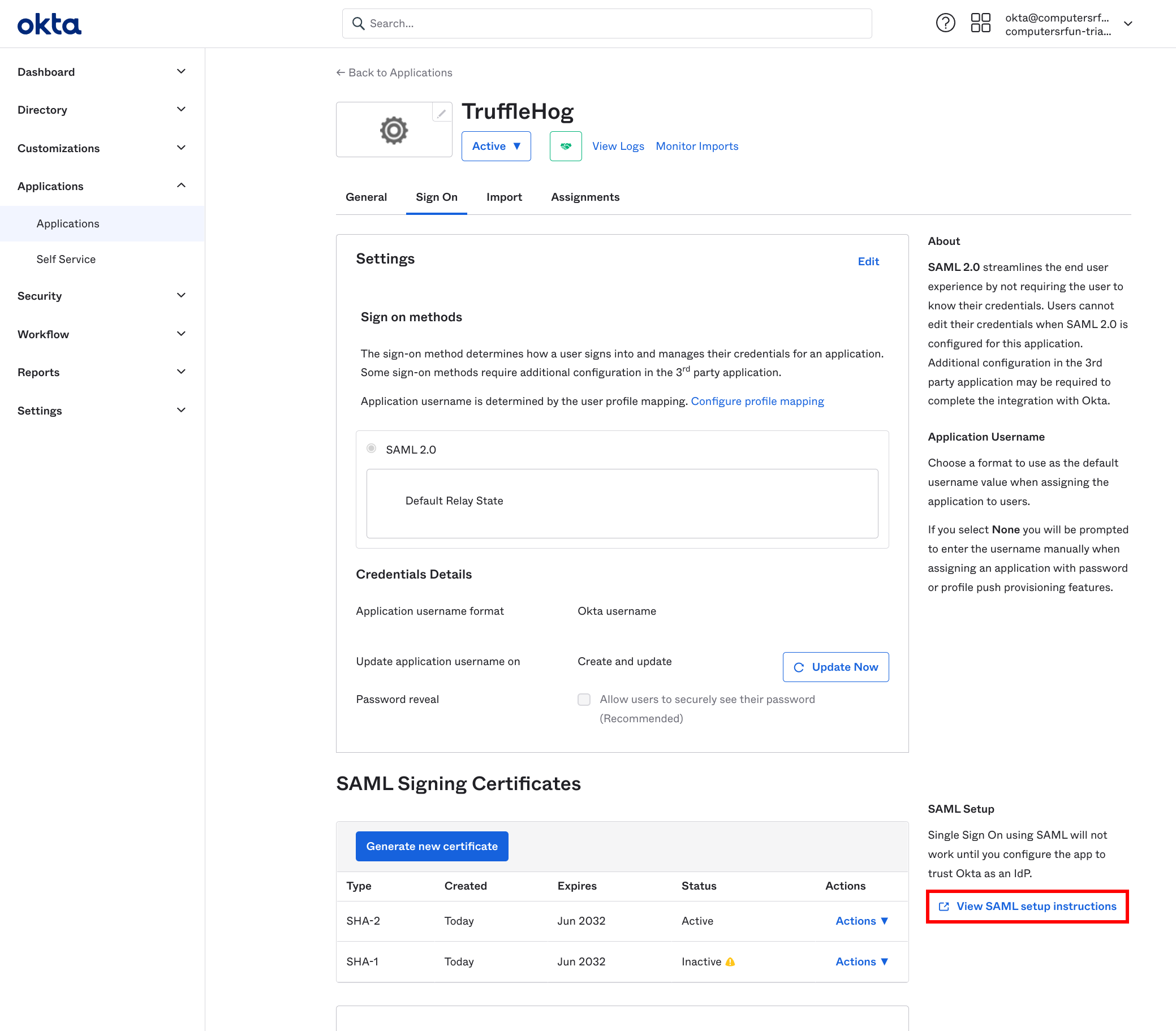
- Select the IDP metadata from the text box
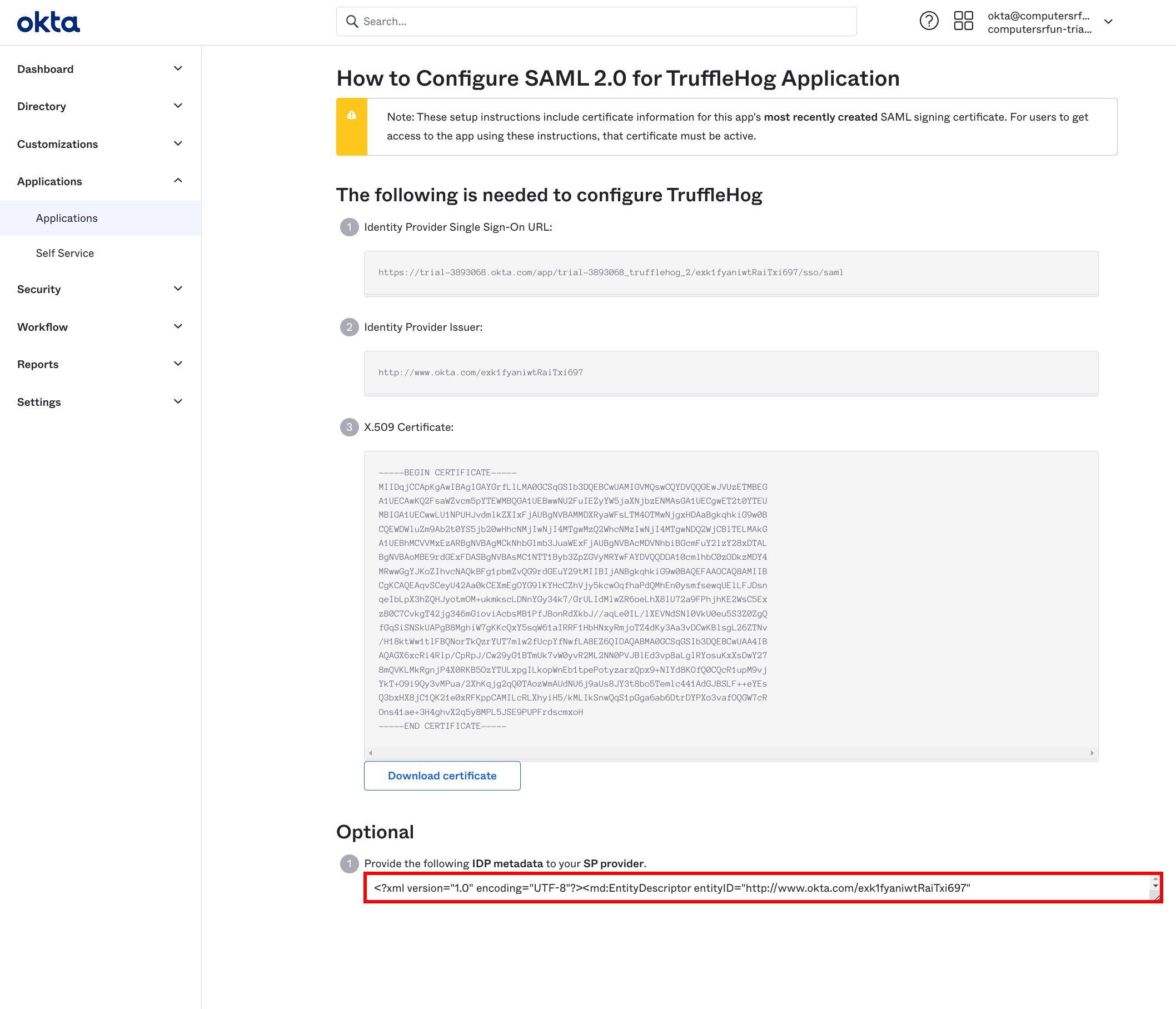
- Paste the metadata content into the metadata field on the TruffleHog authentication page
Azure Configuration
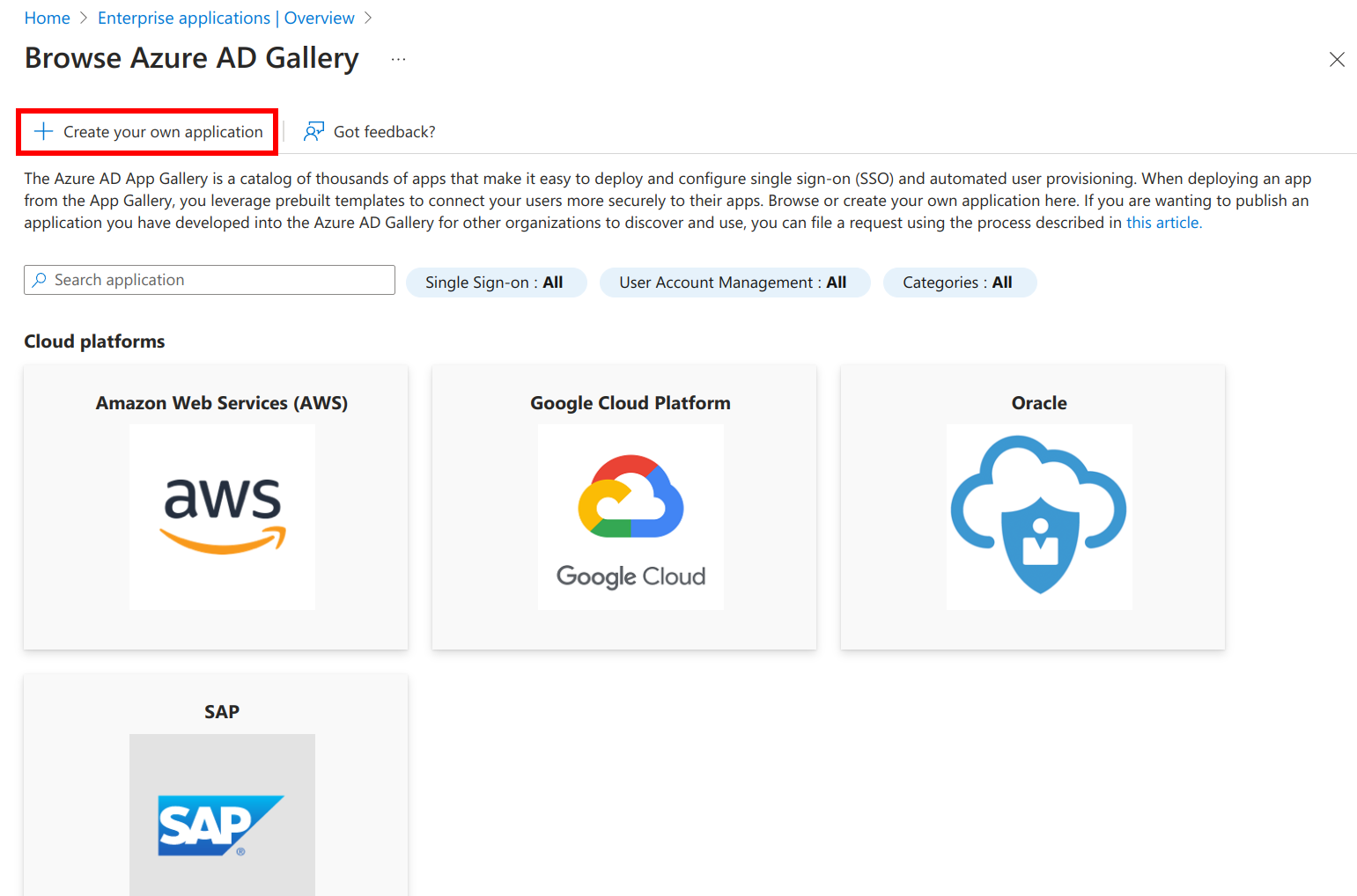
- Go to Enterprise Applications, and select “New Application”
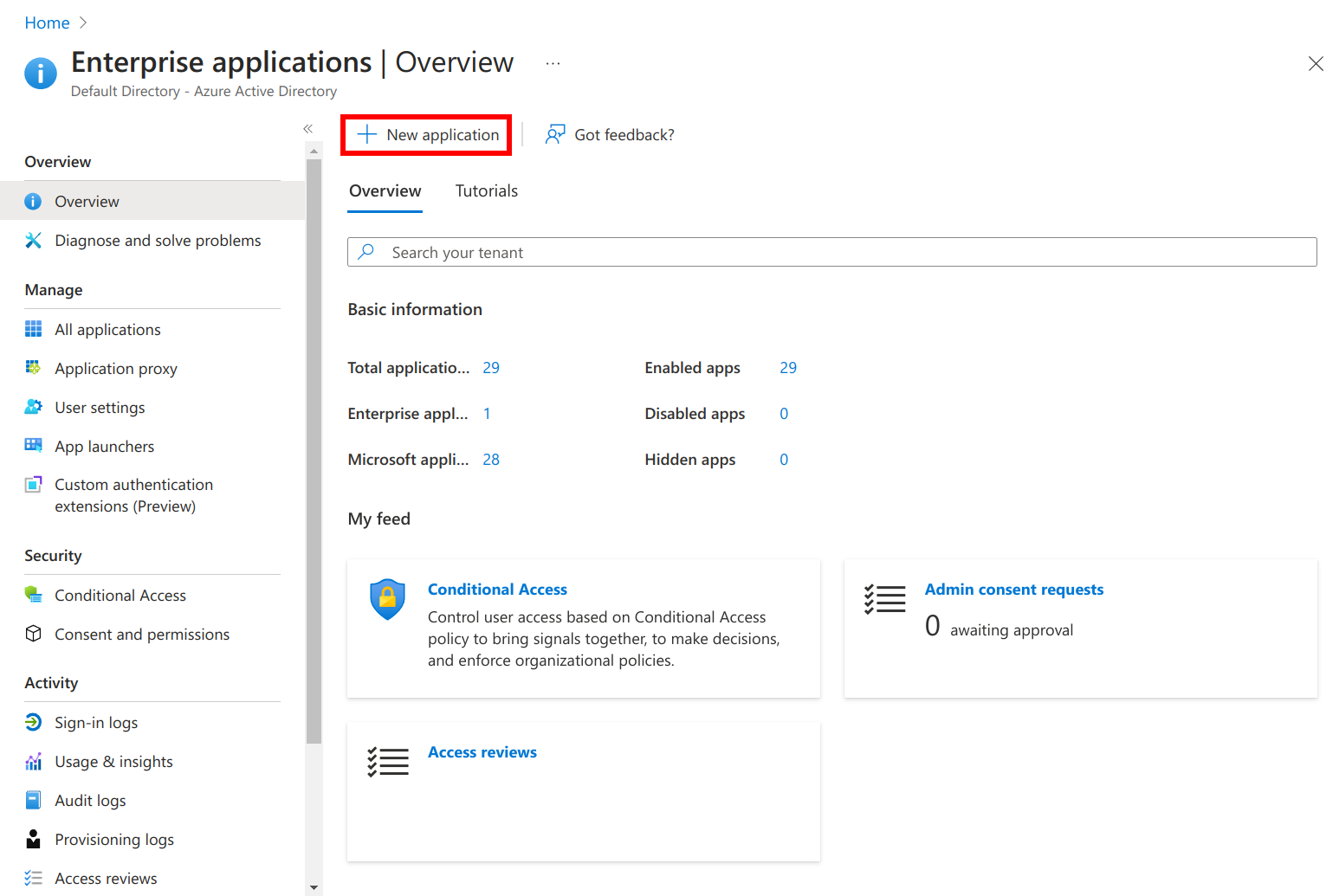
- Select “Create your own application”
- Enter the name of your application, and click Create
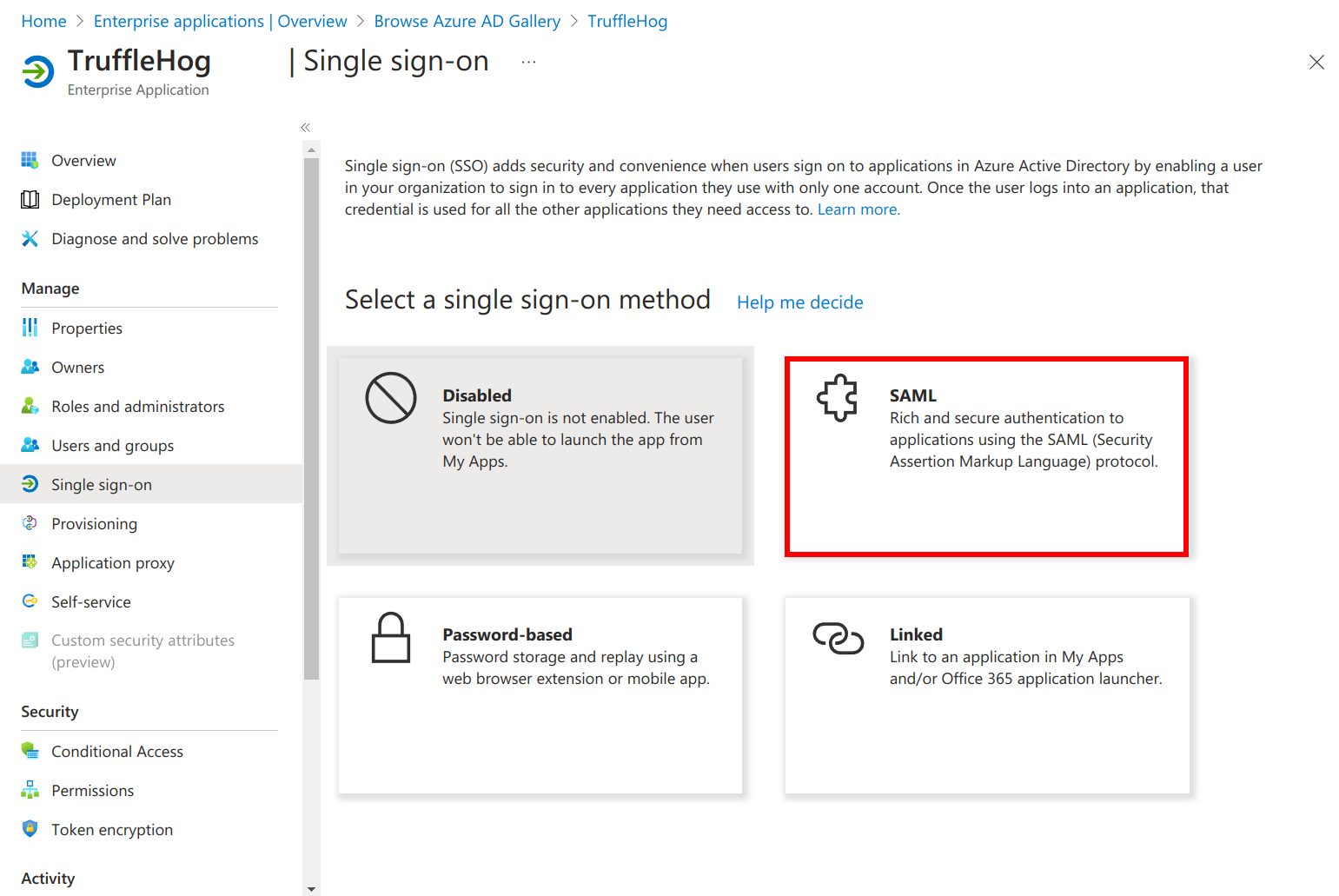
- Go to Single sign-on, and select SAML
- Edit Basic SAML Configuration
- Set Identifier to Audience URI from TruffleHog Authentication Page
- Set Reply URL to ACS URL from TruffleHog Authentication Page
- Save
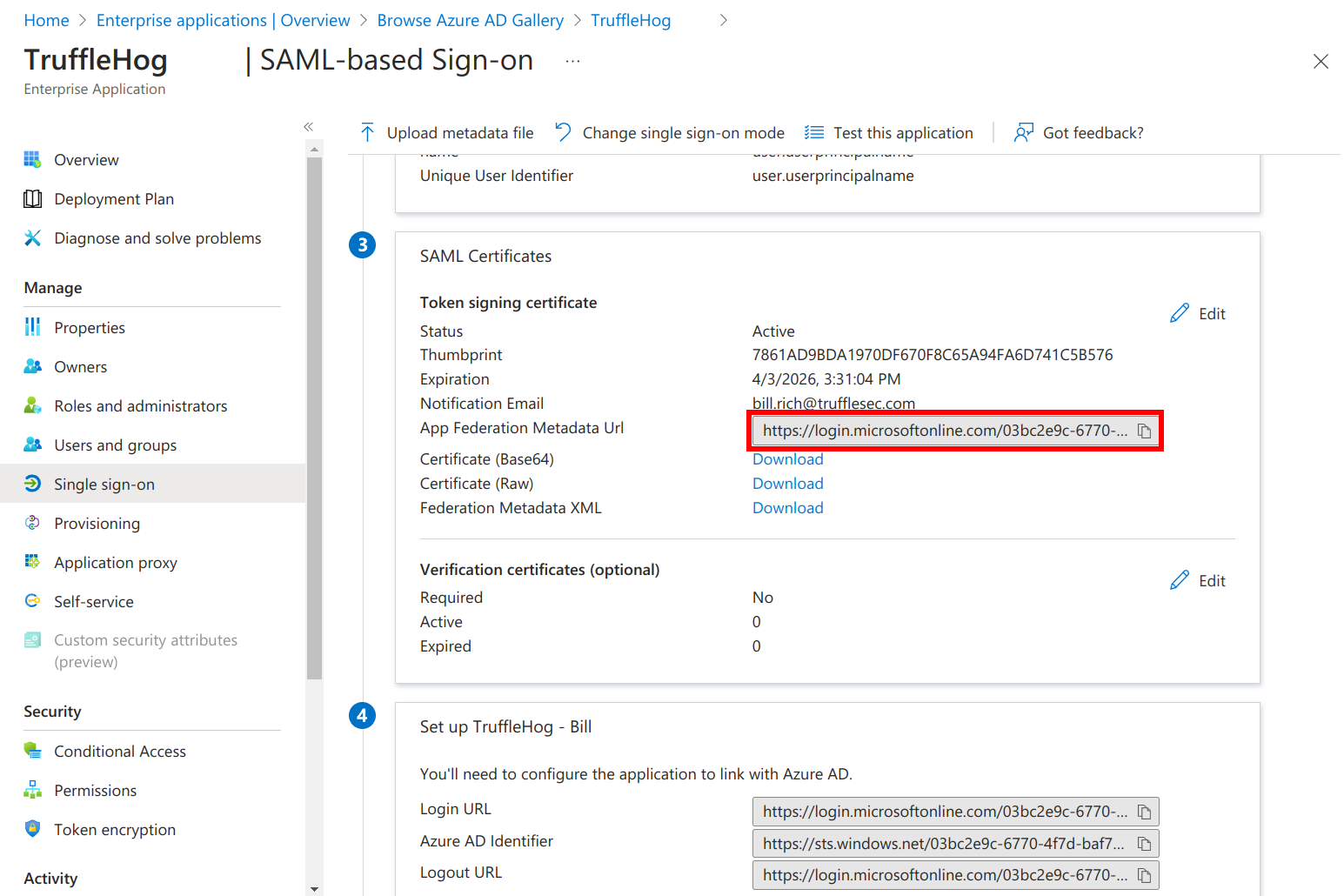
- Go back to Single sign-on, and copy the App Federation Metadata Url and paste the Metadata URL in TruffleHog Authentication Page
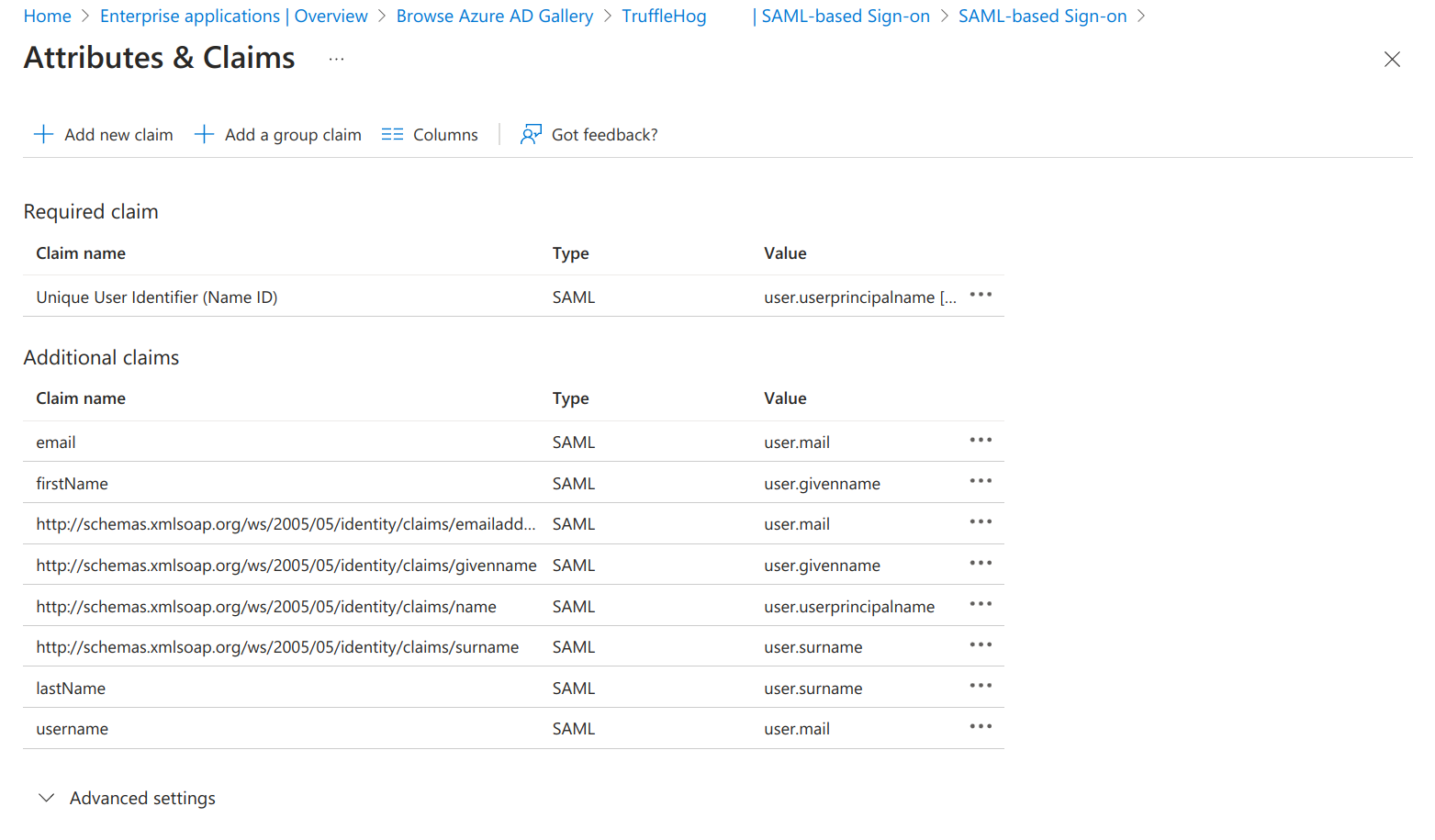
- Edit Attributes & Claims and add the following:
- username: user.mail
- email: user.mail
- firstName: user.givenName
- lastName: user.surname
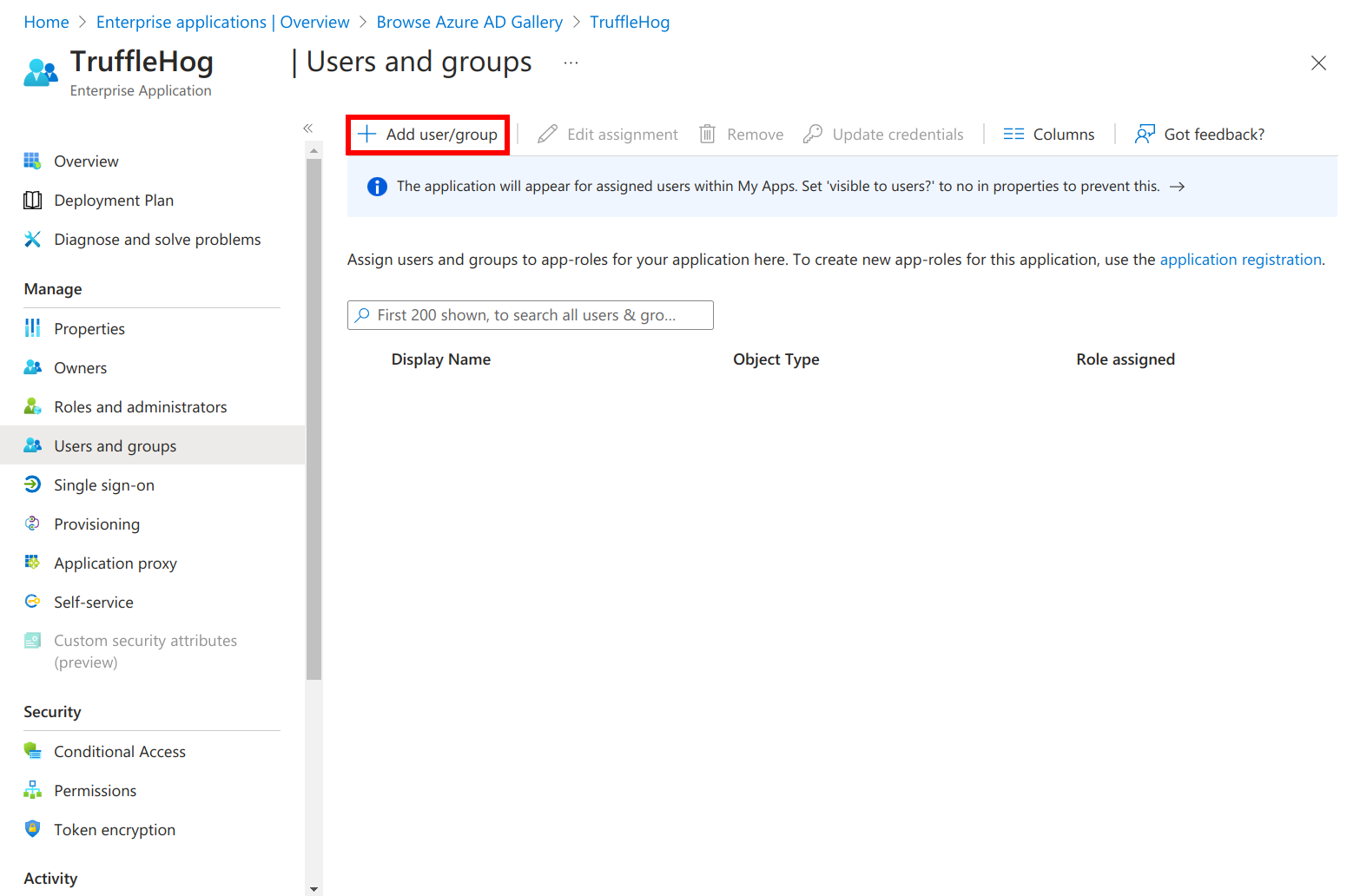
- Add users or groups to your application
Aditional Notes
- If you are using an IdP that uses a subject that is unique for each session, add a ‘username’ attribute/claim that returns the user’s email address.